Revolution of 2001 : Advance Encryption Algorithm
Revolution of 2001 : Advance Encryption Algorithm
Revolution of 2001 : Advance Encryption Algorithm
This algorithm is believed to have changed the standards for encryption algorithm. Established by NIST in 2001 AES is a variation of Rijndael algorithm proposed by two Belgian cryptographers Joan Daemen and Vincent Rijnmen.
It is a symmetric block cipher meaning same key will be used for encryption and decryption and the message is broken into blocks for transmission.
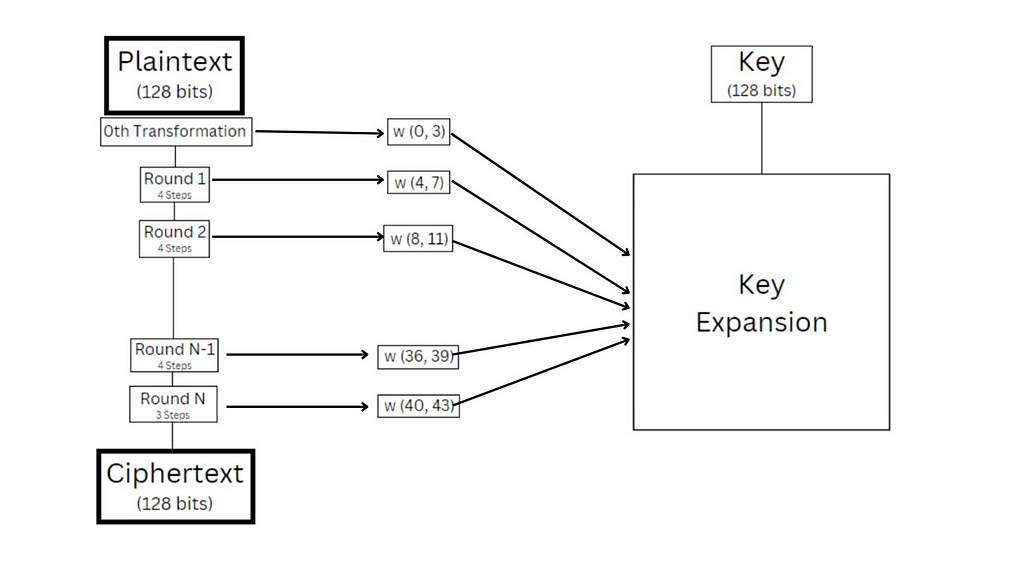
This algorithm makes use of several rounds to encrypt message. It has 3 variations with key size of 128, 192 and 256 respectively, and utilizes 10, 12 and 14 rounds of transformations respectively.
Each round consists for 4 transformations:
- Sub Bytes: This transformation uses a lookup table to substitute values in the block.
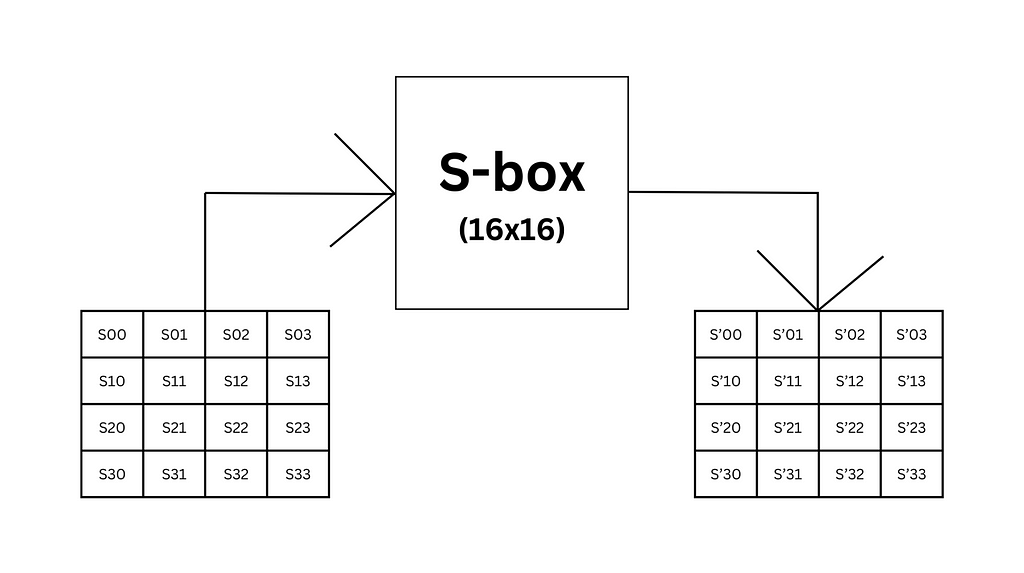
Sub-bytes
2. Shift Rows: This step uses increasing left circular shift to transform matrix.
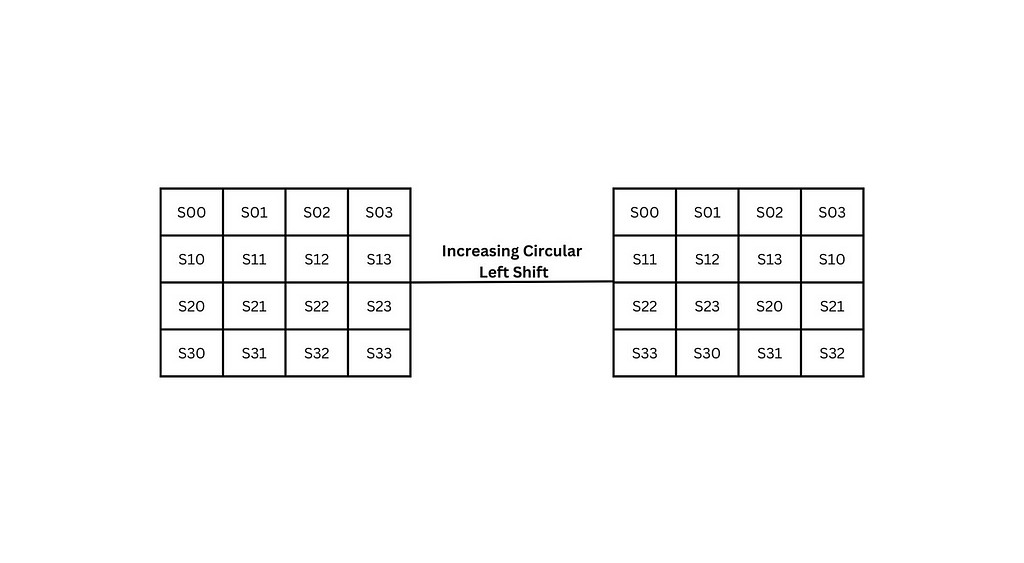
Shift Rows
3. Mix Columns: This transformation uses a pre-defined matrix and using matrix multiplication the result is transformed.
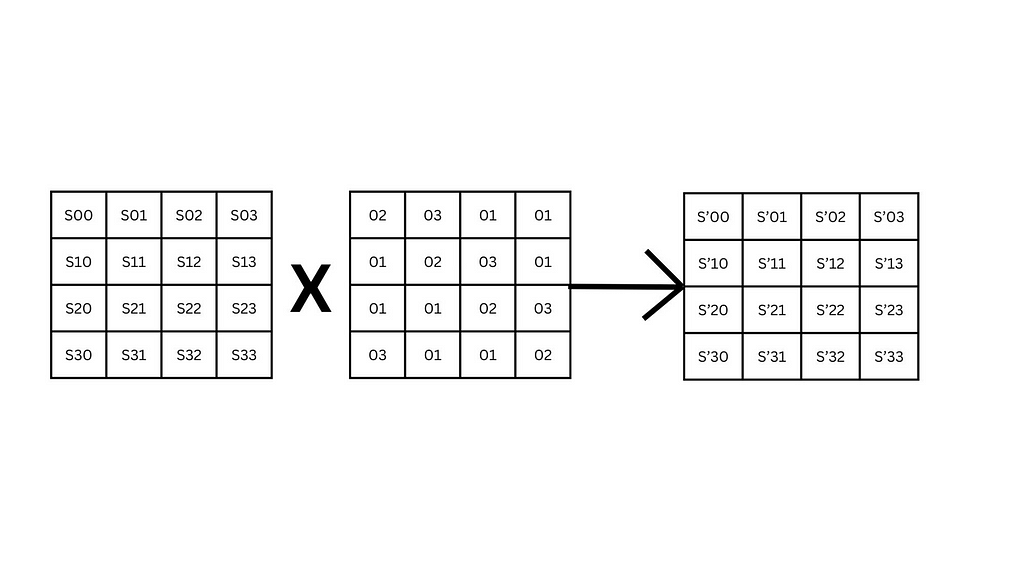
Mix Column
4. Add Round Key: The XOR of round key and block is the result of this transformation.
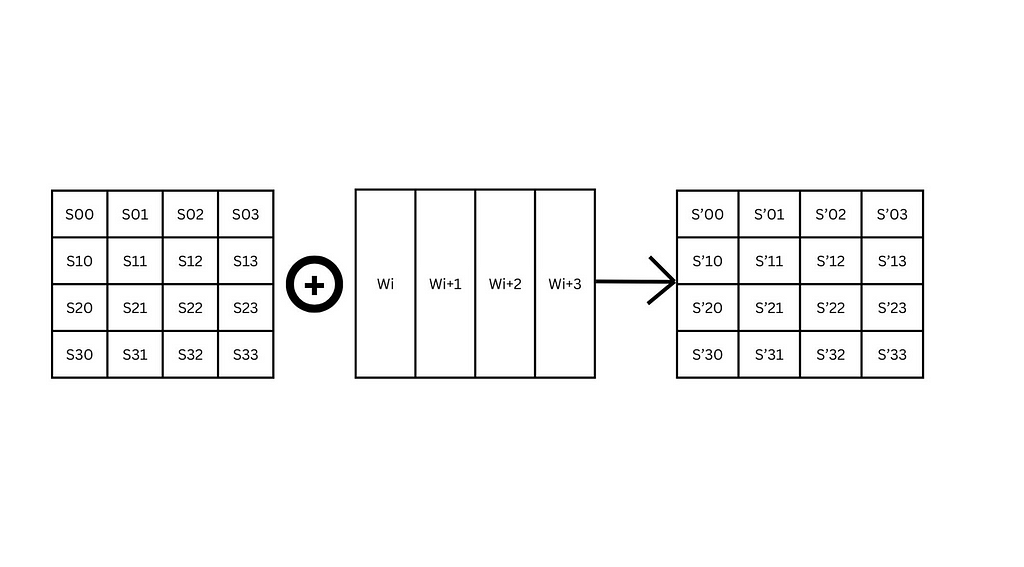
Add Round Key
The 128 bit key is expanded in to be used in every round using the Key Expansion Algorithm. The key expansion algorithm takes this 128-bit key and expands it into 11 round keys, each consisting of 16 bytes (128 bits). I’d recommend watching the video to get a better understanding of the scheduling algorithm.
For decryption we’ll be inversing the operations, ie. we’ll shift rows in an inverse manner and inverse every process in the same manner.
During decryption as well we will not be inverse mixing the columns in the last round. What I forgot to add in the diagram is that every connected block is a round and those rounds are repeated 10 times in AES 128 utilizing the expanded key.
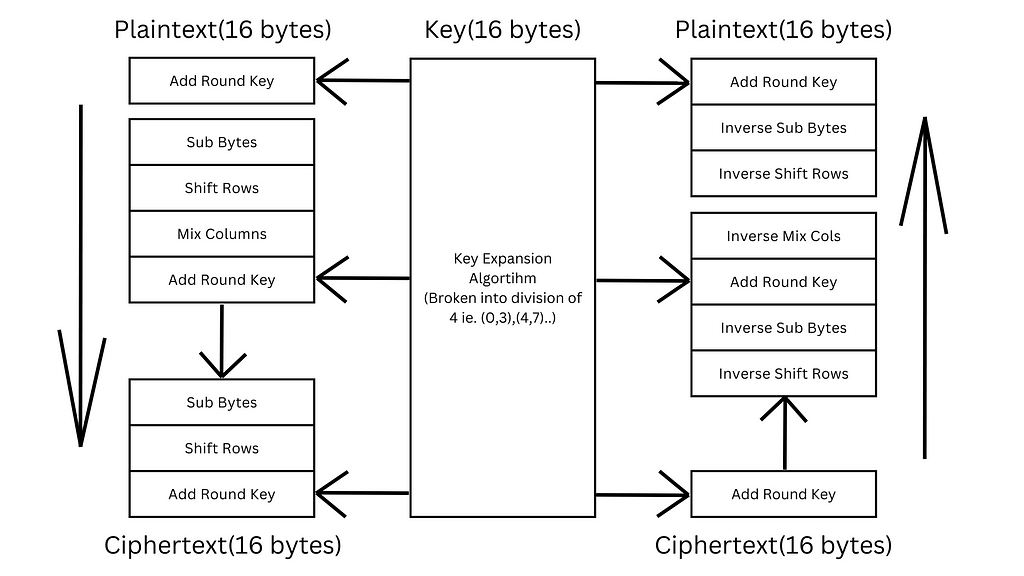
AES Simplified
If K1 key is being used in round 1 of encryption then the K1 key will be used in round 10 of decryption.
As always thanks for reading. Let me know if I have missed something(I have missed a lot).
AI Tools
Related Posts
Is it Occultism or just a Geometric Cryptogram?
Diving deeper into historic cryptograms we also see graphical ciphers. They provided a representational method to hide your message. Such ciphers have been documented for centuries being used in occults and secret societies.
New ways to hide your text for dummies
The easiest way to hide messages is to replace it with something different. And today we’ll be covering such a cipher(if you can call it that).
With Purpose Without Use: Affine Cipher
Although rarely employed in practice, the Affine cipher is a prominent name often encountered in the field of cryptography. In order to understand ...