New ways to hide your text for dummies
The easiest way to hide messages is to replace it with something different. And today we’ll be covering such a cipher(if you can call it that).
The easiest way to hide messages is to replace it with something different. And today we’ll be covering such a cipher(if you can call it that).
Polybius Square was invented by ancient Greeks Cleoxenus & Democleitus. It is a representation method and is used in many other ciphers as well.
It was made famous by Polybius. It is used for fractionating plaintext characters so that they can be represented by a smaller set of symbols used for telegraphy, steganography and cryptography.
This device was originally used for fire signaling, allowing for coded transmission of any message, not just a finite number of predetermined options as was the convention before.
Polybius Square
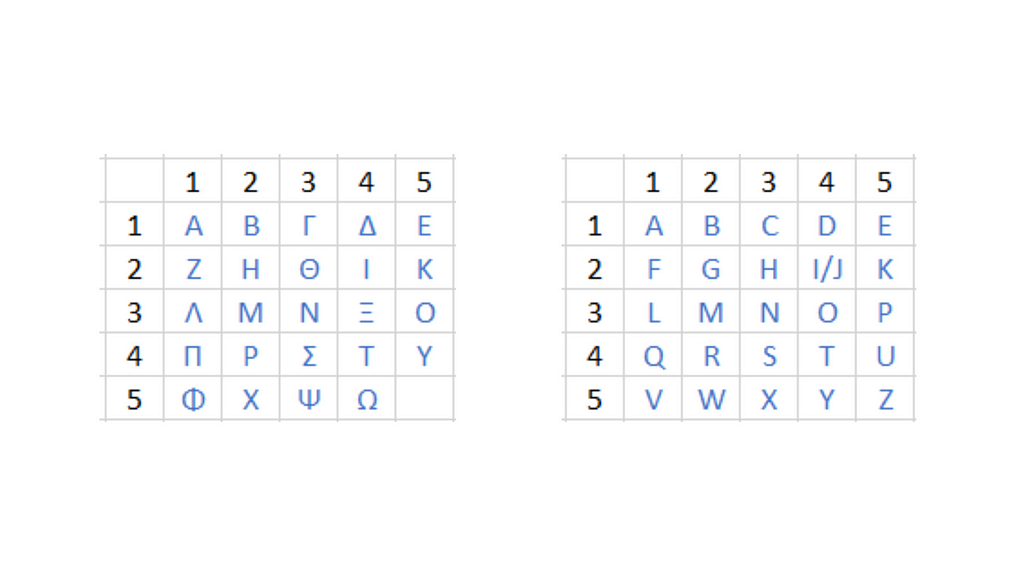
In the above figure the right one corresponds to the Greek letters and in the right are the modern English alphabets in which I and J have to share a space.
There are many ways you can utilize this cipher below I have given 3 variations of polybius cipher.
Encryption Methods:
Method 1:
Locate alphabet and use alphabet just below for lowest go to top.
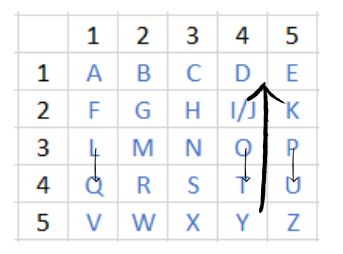
Plaintext: P O L Y B I U S
Ciphertext: U T Q D G O Z X
The plaintext can be retrieved by getting the elements in the Polybius Square lying above the plaintext characters.
Method 2:
Plaintext: P O L Y B I U S
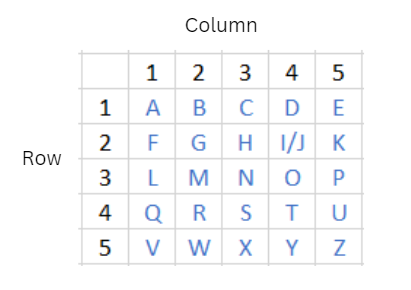
Column: 5 4 1 4 2 4 5 3
Row: 3 3 3 5 1 2 4 4
From the column and row numbers we can form a sequence appending column numbers after row numbers and forming pairs.
54 14 24 53 33 35 12 44
Column: 5 1 2 5 3 3 1 4
Row: 4 4 4 3 3 5 2 4
Cipher: U Q R P N X F T
The cipher produced can be sent to receiver. In order to decode it, trace the rows and columns of the cipher alphabets, create a string by following the zig-zag pattern, distribute it in the same number of columns as the length of the cipher and get the elements from the matrix created.
Method 3:
Taking the sequence we got from method 2.
5414245333351244
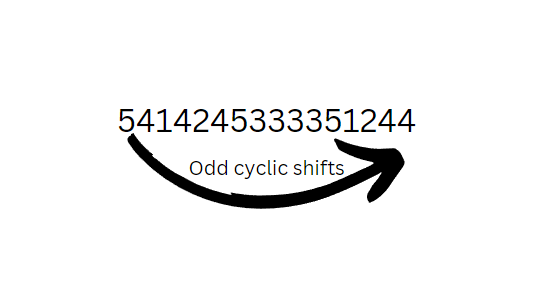
Resulting seq is cyclically shifted to the left by one step(odd number of times)
4142453333512445
Column: 4 4 4 3 3 5 2 4
Row: 1 2 5 3 3 1 4 5
Cipher: D I Y N N E R Y
Cipher can be turned back into plaintext in the same way as the method 2.
Here, I even created a dummy page for you to try out!
AI Tools
Related Posts
Revolution of 2001 : Advance Encryption Algorithm
Revolution of 2001 : Advance Encryption Algorithm
Is it Occultism or just a Geometric Cryptogram?
Diving deeper into historic cryptograms we also see graphical ciphers. They provided a representational method to hide your message. Such ciphers have been documented for centuries being used in occults and secret societies.
With Purpose Without Use: Affine Cipher
Although rarely employed in practice, the Affine cipher is a prominent name often encountered in the field of cryptography. In order to understand ...