With Purpose Without Use: Affine Cipher
Although rarely employed in practice, the Affine cipher is a prominent name often encountered in the field of cryptography. In order to understand ...
Although rarely employed in practice, the Affine cipher is a prominent name often encountered in the field of cryptography. In order to understand the basics of ciphers we need to understand general transformations.
In mathematics, an affine transformation is a combination of linear transformation and translation, that is, x -> ax+b. Affine cipher uses this method for encryption, and it is where most believe the name came from.
One of the first mentions of the Affine cipher was in “Elements of Cryptology” by M. Davio (1983), and J.M. Goethals included the cipher in the book “Secure Digital Communications”.
Affine cipher has found its usage in examples to represent the working of ciphers. It was also recorded by Douglas R. Stinson in “Cryptography: Theory and Practice” (1995).
It is a monoalphabetic substitution cipher, which means that every letter of the message is encrypted individually.
Encryption: Cᵢ = ( ( Pᵢ * A ) + B ) % 26
Decryption: Pᵢ = ( ( Cᵢ — B ) * A⁻¹) % 26
It offers no obvious advantage over combinations of shifts and non-linear permutations, and they have the obvious disadvantage that modular multiplication is far harder to implement mechanically than simple shift. And as hand cipher these are too complex and require lookup tables.
In order to use this encryption, we require two keys A and B which must be coprime. And in order to decrypt it we require inverse of A, that is, A⁻¹.
Plain Text: HELLO
A: 7, B: 2
Cipher Text: ZEBBW
Encryption:
Each letter of the plaintext is convert to represent numbers for example A:0, B:1, C:2, D:3, … Z:25. After the conversion we apply multiplicative and additive transformation to each character.
The result of every transformation is again converted to alphabets using same pattern.
P1 = ((7*7)%26+2)%26 = 25->Z
P2 = ((4*7)%26+2)%26 = 4->E
P3 = ((11*7)%26+2)%26 = 1->B
P4 = ((11*7)%26+2)%26 = 1->B
P5 = ((14*7)%26+2)%26 = 22->W
Decryption:
In order to decrypt the cipher text we require A⁻¹.
As 7x%26 = 1
We can use brute force approach or Extended Euclidean Algorithm to find the inverse.
A⁻¹ = 15
After finding the inverse we use the formula to find the plain text alphabets.
C1 = ((25–2)%26)*15)%26 = 7->H
C2 = ((4–2)%26)*15)%26 = 4->E
C3 = ((1–2)%26)*15)%26 = 11->L
C4 = ((1–2)%26)*15)%26 = 11->L
C5 = ((22–2)%26)*15)%26 = 14->O
This cipher isn’t good for anything in practice. The keyspace is not that much larger than that of simple Caeser shift ciphers, and in any case, they are just as vulnerable to attacks via frequency analysis as any other simple monoalphabetic substitution cipher.
Yet it is a cipher which provides a better understanding of the transformations which are frequently used in cryptography.
Try out Affine Cipher!
AI Tools
Related Posts
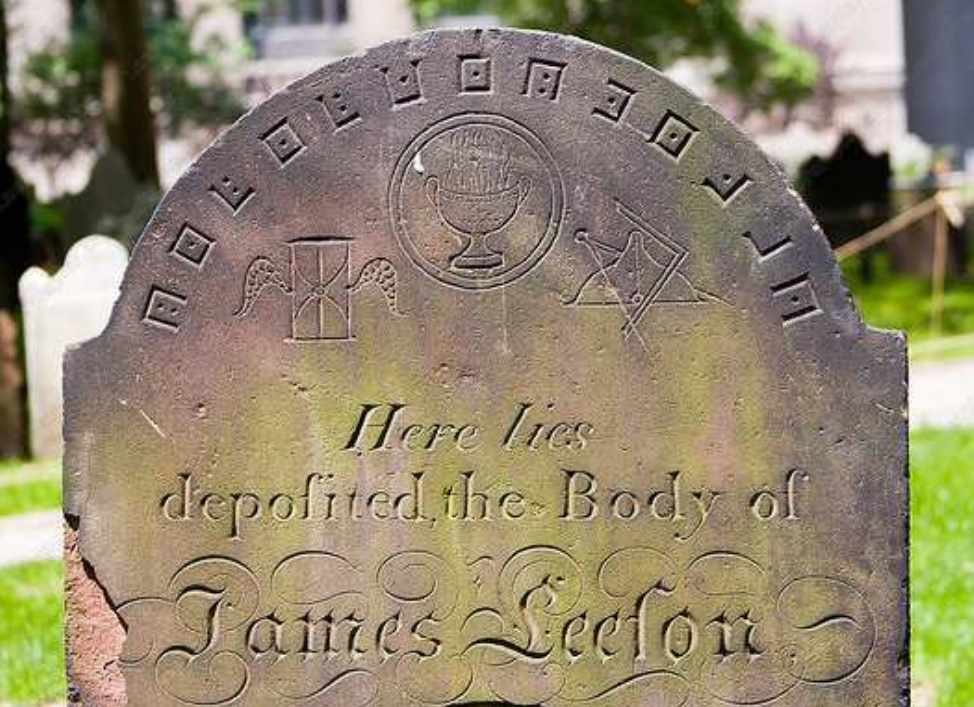
Is it Occultism or just a Geometric Cryptogram?
Diving deeper into historic cryptograms we also see graphical ciphers. They provided a representational method to hide your message. Such ciphers have been documented for centuries being used in occults and secret societies.

Tool of Historic and Modern Espionage: Steganography
Throughout history, we have been trying to find ways to hide information, but it has rarely been adequate in practice. This time I came across a ra...

Unveiling the Story and Significance of the RSA Algorithm
Let’s talk about one of the most famous algorithms in cybersecurity, the RSA algorithm. As simple as it is, it has yet to be broken. It was created...