Keeping it Simple with Railfence Cipher Encryption
Now, obviously, not all ciphers can be perfect and secure, so today we will be understanding a rather easy-to-understand cypher, the Railfence Ciph...

Scytale
Now, obviously, not all ciphers can be perfect and secure, so today we will be understanding a rather easy-to-understand cypher, the Railfence Cipher. It is a transposition cipher, where characters are permuted to encrypt the message.
The use of this cipher dates back to the ancient Greeks, who used to encrypt their messages using a tool known as ‘scytale’. It was a transposition machine consisting of a cylinder with a ribbon wrapped around it. In order to encrypt, the message is written across the coiled ribbon, and when it is uncoiled, the letters of the message get rearranged. It can be deciphered easily by wrapping the ribbon along the cylinder. In this cipher the diameter of the cylinder is the key to encrypting and decrypting, as differences in diameter might result in different ciphers.
In the same manner as in the Railfence cipher, we use the number of rows as the key to encrypt the message. It transfers the same properties as scytale. It works by generating a matrix with a zig-zag pattern and a fixed number of rows.
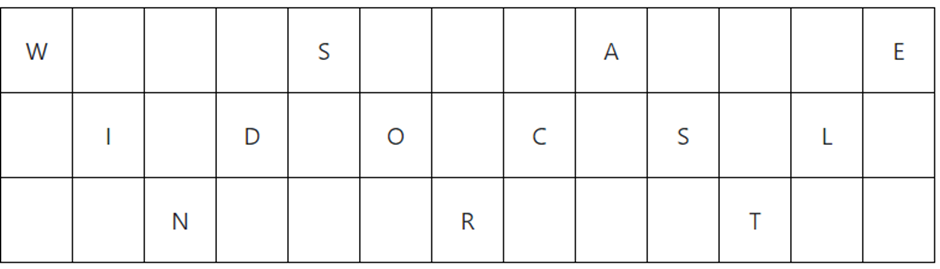
After forming a 2D matrix or table, we write a letter in a row-wise manner, thus creating the cipher.
Plaintext: WINDSORCASTLE
Key: 3
Ciphertext: WSAEIDOCSLNRT
Below is a implementation of the Railfence cipher.
https://medium.com/media/d9086e2b237944e21ba2513b3cb88e99/hrefIn order to decrypt a Railfence cipher, we must know the key in order to put the cipher in the correct order to retrieve the message.
It wasn’t necessarily a secure way of communication yet it was used by both sides during the American Civil War as a field cipher due to its effortless nature.
Try out Railfence Cipher!
AI Tools
Related Posts

Living in the shadow of Vigenère: Beaufort Cipher
Considered widely a variation of the Vigenère Cipher, the Beaufort Cipher is also a polyalphabetic substitution cipher that makes use of a lookup table when being encoded and decoded by hand.

Unveiling the Story and Significance of the RSA Algorithm
Let’s talk about one of the most famous algorithms in cybersecurity, the RSA algorithm. As simple as it is, it has yet to be broken. It was created...
Revolution of 2001 : Advance Encryption Algorithm
Revolution of 2001 : Advance Encryption Algorithm